 Visual Paradigm Desktop |
Visual Paradigm Desktop |  Visual Paradigm Online
Visual Paradigm OnlineEngineering systems that power aviation, healthcare, defense, and infrastructure requires a level of precision that traditional documentation methods often struggle to maintain. As complexity grows, the risk of ambiguity increases. This is where the Systems Modeling Language (SysML) becomes indispensable. However, creating a model is only the beginning. The true value lies in verifying that the model accurately represents the intended system behavior and satisfies all critical requirements. This guide outlines a comprehensive approach to establishing a verification strategy within a Model-Based Systems Engineering (MBSE) framework.
Verification answers the question: Are we building the product right? In the context of SysML, this means ensuring that the model itself is correct, consistent, and complete relative to the defined requirements and design specifications. It is distinct from validation, which asks if we are building the right product. Verification focuses on the internal logic, syntax, and semantic correctness of the diagrams and requirements.
Without a rigorous verification strategy, models can drift from their original intent. A block definition diagram might show a connection that is physically impossible. An activity diagram might describe a sequence that leads to a deadlock. These errors are costly if discovered late in the development lifecycle. Therefore, verification must be integrated early and often.
Mission-critical systems differ from commercial products in their tolerance for failure. In these sectors, a failure can result in loss of life, significant financial damage, or national security risks. Consequently, the verification strategy must be more rigorous than standard software testing protocols.
The following factors define the high-stakes environment:
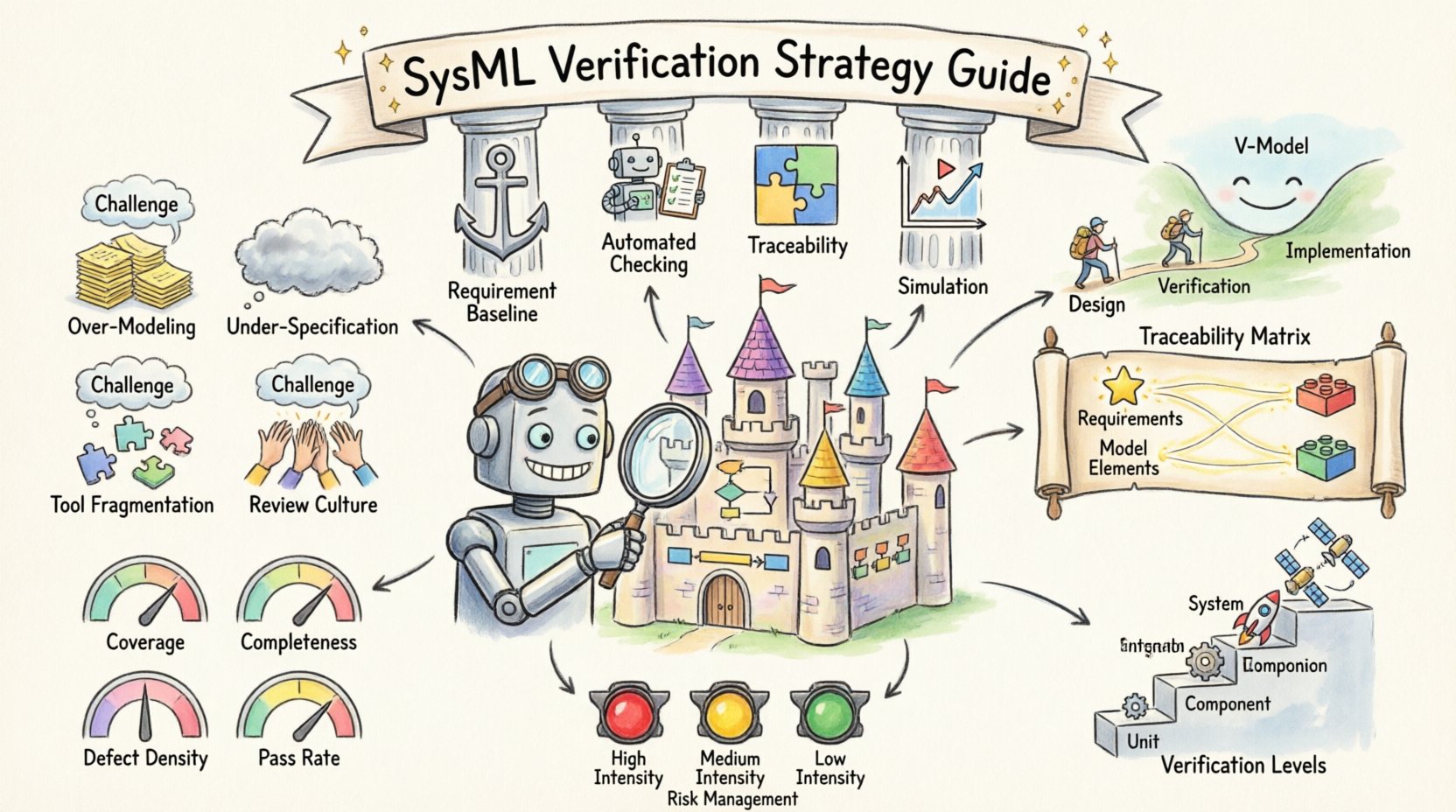
A successful strategy rests on four foundational pillars. Neglecting any one of these can compromise the integrity of the entire delivery.
Verification cannot begin if requirements are fluid. While changes are inevitable, the verification process requires a stable baseline. You must define change control procedures that ensure any modification to a requirement triggers a review of associated model elements.
Manual review is prone to human error. Automated tools should be employed to check for common modeling errors. This includes checking for orphaned blocks, unconnected ports, and circular dependencies. Automation allows engineers to focus on logic rather than syntax.
Traceability links requirements to design elements. In SysML, this is often achieved through Requirement Diagrams and Traceability relationships. A strong strategy ensures that every requirement has a verification status (Pass, Fail, or Not Verified).
SysML models are static representations. To verify dynamic behavior, simulation is often required. Parametric diagrams can be used to verify physical constraints, while activity diagrams can be analyzed for logical flow. Simulation bridges the gap between abstract design and concrete behavior.
The verification plan is the document that governs the entire process. It defines the scope, resources, schedule, and methods for verification. It should not be a static document but a living artifact that evolves with the project.
| Element | Description | Importance Level |
|---|---|---|
| Scope | Defines which models and requirements are included. | Critical |
| Tools | Specifies the modeling and analysis environments used. | High |
| Roles | Identifies who performs verification (engineers, reviewers, auditors). | High |
| Metrics | Defines how success is measured (coverage, defect rate). | Medium |
| Entry/Exit Criteria | Conditions required to start and end verification activities. | Critical |
Execution involves running the checks defined in the plan. The goal is to generate evidence that the model meets the requirements. This evidence is crucial for certification and auditing.
The Traceability Matrix is the central artifact for tracking verification status. It links every requirement to the specific model element that satisfies it. In a SysML environment, this is often a direct relationship within the model itself.
Different levels of verification apply to different parts of the model. The table below outlines the typical hierarchy.
| Level | Focus | Typical Activity |
|---|---|---|
| Unit Verification | Individual Blocks/Attributes | Attribute consistency, Parameter constraints |
| Component Verification | Subsystems | Interface compatibility, Internal logic flow |
| System Verification | Full Architecture | End-to-end requirements, Scenario simulation |
| Integration Verification | External Interfaces | Hardware-in-the-loop, Environmental stress |
How do you know the strategy is working? You need quantitative metrics. These metrics provide visibility into the health of the project and the quality of the models.
Even with a well-defined plan, organizations face hurdles. Recognizing these pitfalls early allows for proactive mitigation.
Creating detailed models for areas that are not critical to the system’s core function wastes time and resources. Focus verification effort on high-risk and high-complexity areas.
Requirements that are vague make verification impossible. If a requirement says “The system shall respond quickly,” there is no metric to verify. Requirements must be measurable and unambiguous.
Using different tools for requirements, modeling, and testing can break traceability. Ensure the ecosystem supports data exchange and maintains links across the lifecycle.
Automation is powerful, but it cannot replace human judgment. Peer reviews of the model are essential to catch logical errors that scripts might miss.
Verification should not be a separate phase at the end of the project. It must be integrated into the development lifecycle. The V-Model is a common framework for this integration.
| Left Side (Design) | Center (Verification) | Right Side (Implementation) |
|---|---|---|
| System Requirements | System Verification | System Integration |
| System Architecture | Architecture Verification | System Integration |
| Component Design | Component Verification | Component Testing |
| Module Design | Module Verification | Unit Testing |
By aligning SysML verification activities with this structure, teams ensure that design decisions are validated before code or hardware is produced. This reduces rework costs significantly.
Beyond basic checks, advanced techniques can provide deeper insights into system behavior.
These diagrams allow engineers to model physical constraints and mathematical relationships. They are essential for verifying performance requirements such as power consumption, thermal limits, or stress tolerances. Solving the equations within these diagrams provides proof that the design meets physical laws.
For systems with complex logic, State Machine Diagrams are vital. Verification here involves checking for deadlocks, unreachable states, and proper transition logic. It ensures the system behaves correctly under all possible conditions.
Define use cases that represent real-world usage. Model these scenarios in the SysML environment to see if the system handles them as expected. This helps uncover edge cases that might not appear in standard functional testing.
Verification effort should be proportional to risk. Not all requirements carry the same weight. A safety-critical requirement requires a higher level of verification than a cosmetic one.
By mapping risk to verification effort, teams can optimize resources while maintaining safety standards.
Mission-critical systems often outlive the teams that built them. The verification artifacts must be maintainable. This means:
Adopting a SysML verification strategy is a cultural shift. It moves the organization from document-centric to model-centric engineering. This transition requires discipline, training, and a commitment to quality. The benefits, however, are substantial: reduced risk, lower costs, and higher confidence in the final product.
Success depends on consistent application of the strategy. It is not a one-time activity but a continuous process that runs parallel to development. By embedding verification into every step of the workflow, organizations can deliver mission-critical systems with the reliability they demand.
Remember that the model is a tool for communication as much as it is a specification. A verified model is a verified understanding of the system. This shared understanding is the foundation of successful system delivery.